Dental IT Support: What Dentists Should Look for in an MSP
Running a dental practice today means managing far more than patient care.
You’re balancing schedules, staff workflows, compliance requirements, and a growing set of digital systems that keep the operatory moving.
When something breaks — a sensor stops responding, imaging software freezes, or the server hosting your charts goes down — the impact is immediate. Appointments slow. Staff scramble. Patients feel it.
That’s why dental IT support isn’t just an IT decision. It’s an operational one.
The right Managed IT Service Provider (MSP) keeps your practice running smoothly behind the scenes. The wrong one becomes another source of disruption.
Table of Contents
Dental Software Expertise Isn’t Optional — It’s Part of How We Serve Our Local Practices
Dental practices don’t operate like typical office environments.
They rely on tightly integrated systems where imaging, charting, scheduling, and patient communication all depend on each other working seamlessly.
In our local dental community in Omaha, we’ve built our support approach around that reality.
We regularly work with environments powered by:
- Oryx, Open Dental, and EagleSoft
- Sidexis, Dexis, XVCapture, and Pano
- MouthWatch and other intraoral cameras
- Ortho2 orthodontic systems
- Modento patient communication tools
- Sensors, pano, and CBCT integrations
But the real value isn’t just familiarity with names on a screen.
It’s understanding what matters most inside a practice:
- Imaging must work when a patient is in the chair.
- Charting can’t lag during treatment.
- Scheduling interruptions ripple through the entire day.
- Vendor coordination shouldn’t fall on your front desk.
Our role as a managed IT service provider isn’t to “figure it out” when something breaks.
It’s to understand your systems well enough that problems are prevented — and resolved quickly when they do occur.
That’s how trust is built locally. Not through promises, but through consistent, informed support where production time is protected.
Compliance and Security That Protects Patient Trust
Dental practices handle sensitive patient data every day. A security incident isn’t just a technical problem — it’s a compliance, reputational, and operational issue.
Strong dental IT support should include:
- Encrypted data storage and backups
- Secure email and phishing protection
- Multi-factor authentication
- AI automation from patient calls to X-ray reviews
- Network security (staff vs. guest Wi-Fi and HIPPA compliance testing)
- Regular vulnerability reviews
HIPAA-aligned security practices aren’t about checking boxes — they’re about protecting patient trust and keeping your practice out of reactive situations.
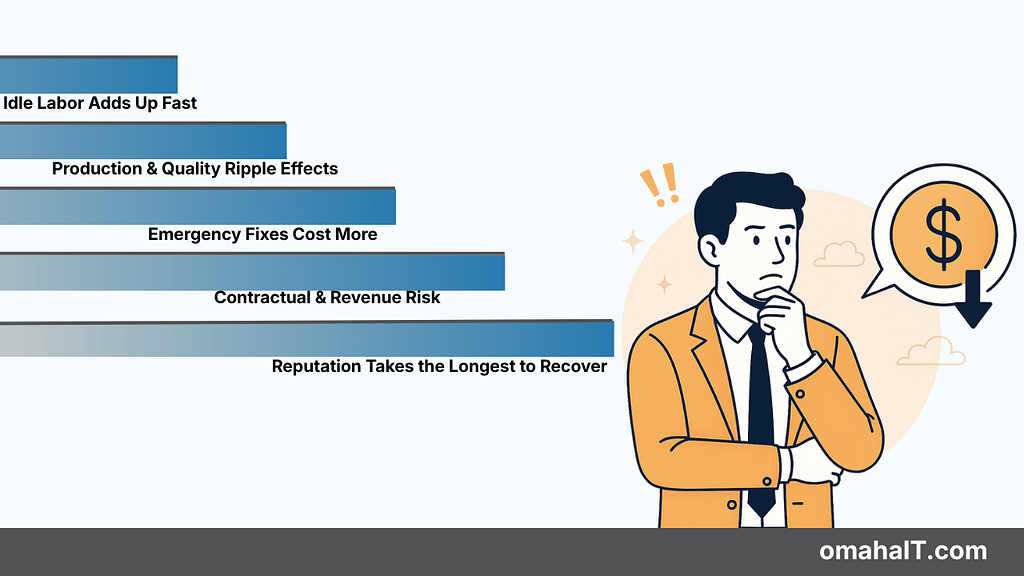
Downtime Prevention (Because Every Chair Matters)
In dentistry, downtime is visible. One operatory offline can disrupt an entire day.
Instead of reacting after something fails, look for dental IT support that focuses on prevention:
- Proactive monitoring of servers, workstations, and imaging devices
- Fast remote response during clinic hours
- Clear escalation paths for urgent issues
- Redundancy for critical systems
The real value of an MSP isn’t how fast they respond — it’s how often you don’t need them.
IT That Fits the Way Dental Teams Actually Work
Dental practices have a rhythm. Assistants move quickly between rooms. Imaging needs to load instantly. Charting must be reliable.
An experienced dental IT provider understands:
- How operatories are laid out
- How imaging integrates with charting and scheduling
- How to schedule maintenance without interrupting patient flow
- How to support peak hours without slowing the team down
Technical knowledge matters — but so does respect for how clinics operate.
Support That’s Present — Not Just Available
Dental practices aren’t generic office environments. They’re physical spaces with operatories, imaging rooms, front desks, and tightly coordinated workflows.
Supporting that kind of environment requires more than remote access, but on-site support.
While many issues can be handled quickly from afar, there are moments when being onsite matters — validating equipment, coordinating with vendors, reviewing infrastructure, or simply understanding how the practice actually runs.
Relationship-driven IT support means being close enough to step in when needed — not just logging in from a distance.
Presence builds familiarity. Familiarity builds trust. And trust protects production time.
Honest Guidance, Not Constant Upselling
Technology decisions in a dental practice carry real cost. The right MSP acts as an advisor, not a reseller.
That means helping you decide:
- When upgrades are necessary — and when they’re not
- Whether cloud, on-premises, or hybrid setups make sense
- Which patient communication tools are secure and practical
- How to modernize without overspending
Good dental IT support provides clarity, not pressure.
Transparent Pricing and Predictable Costs
Surprise invoices erode trust quickly.
A reliable dental MSP should clearly explain:
- What’s included in monthly support
- What’s considered out of scope
- Whether imaging devices are covered
- Emergency or after-hours availability
- Contract terms and exit options
Predictability matters more than the lowest price. Stability keeps practices running.
Backup and Disaster Recovery You Can Actually Rely On
Practice data is irreplaceable. Charts, images, and treatment plans are your lifeline.
Dental IT support should include:
- Automated, daily backups
- Multiple restore points
- Offsite, encrypted storage
- Documented recovery timelines
- Regular backup testing
A backup that hasn’t been tested isn’t a backup — it’s a risk.
Support That Scales as Your Practice Grows
Even if expansion isn’t immediate, your IT should be ready when the time comes.
Look for an MSP that can support:
- Multi-location practices
- Standardized system configurations
- Secure remote access for owners
- Centralized data and reporting
- Scalable storage and networking
Growth shouldn’t require replacing your IT partner.
Clear, Human Communication
Dentists don’t need technical lectures. They need clear answers.
Strong dental IT support communicates:
- In plain language
- With respect for your time
- Proactively, not reactively
- Without hiding behind jargon
Good communication builds confidence. Consistent communication builds trust.
Vendor Coordination Without Finger-Pointing
Dental IT often involves multiple vendors — equipment suppliers, imaging providers, software companies.
A capable MSP should:
- Coordinate directly with vendors
- Manage updates safely
- Help navigate warranty issues
- Take ownership of integration problems
You shouldn’t be caught in the middle of technical blame games.
Final Thoughts: Dental IT Support Should Feel Like a Partnership
Choosing dental IT support isn’t about finding the flashiest MSP or the cheapest package. It’s about finding a partner who understands the pace, pressure, and expectations of running a dental practice.
When IT works quietly in the background, your team stays focused on patient care.
When it doesn’t, everything feels harder than it should.
The right dental MSP brings stability, clarity, and confidence — so technology supports your practice instead of slowing it down.
If you’re unsure whether your current IT setup is truly supporting your practice — start with clarity.
A practical review can reveal where risk, friction, or downtime might be hiding.

Dental IT Support: What Dentists Should Look for in an MSP Read More »