How to Know If Your IT Budget Is Too Low — and Where Underfunding Hurts First
Most leaders do not begin their day concerned that their IT budgets are too low.
At first glance, all appears to be in order: systems remain operational, support tickets are resolved, and there have not been any significant incidents prompting difficult discussions. When observed from a distance, it may seem that technology is effectively managed.
But under the surface, subtle cracks often start to form — and they almost always show up in the same places first.
Teams spend more time firefighting than improving. Security alerts linger longer than they should. Projects stall because no one has the time, tools, or breathing room to move them forward.
When that pattern emerges, it’s rarely about effort or competence. It’s a sign the IT budget is too low for the level of risk, complexity, and expectations the organization is carrying.
The challenge is that IT underfunding doesn’t announce itself clearly. It doesn’t show up as a single broken system or a line item that’s obviously wrong. It shows up operationally first — long before leadership labels it a budgeting problem.
Research shows that many organizations struggle to link IT spend directly to business outcomes and operational performance, meaning issues from inadequate budgeting often surface first in day-to-day operations rather than as a clear “budget problem.”
For example, only a small minority of businesses believe their IT budgets are fully optimized — with 95 % saying they are not fully optimized and many actively reviewing or cutting IT spending even as overall spend grows — suggesting that underfunding pressures are widespread and not immediately obvious until operational strains appear.
This article walks through how to recognize those early signals, where underfunding tends to hurt first, and how to prioritize fixes without turning IT budgeting into guesswork.
Table of Contents
Why IT Underfunding Rarely Looks Like a Budget Problem
Most IT budgets are built backward.
They’re based on last year’s spend, last year’s incidents, and last year’s sense of urgency. If nothing catastrophic happened, the assumption is often that the budget was “about right.”
But the environment rarely stays still.
- Security requirements increase quietly
- Infrastructure ages
- Compliance expectations expand
- Workflows become more dependent on systems
- Teams expect faster turnaround with fewer disruptions
When budgets stay flat while complexity grows, the gap doesn’t show up immediately. It shows up as friction.
Things still work — just not smoothly.
Issues get resolved — just not quickly.
Projects move forward — just not on schedule.
From a leadership perspective, that friction often gets misdiagnosed as execution problems, staffing issues, or growing pains. In reality, it’s frequently the first sign that the organization has outgrown its current IT funding level.
When budgets stay flat while complexity grows, the gap doesn’t show up immediately. It shows up as friction.
The First Places an IT Budget Falls Short
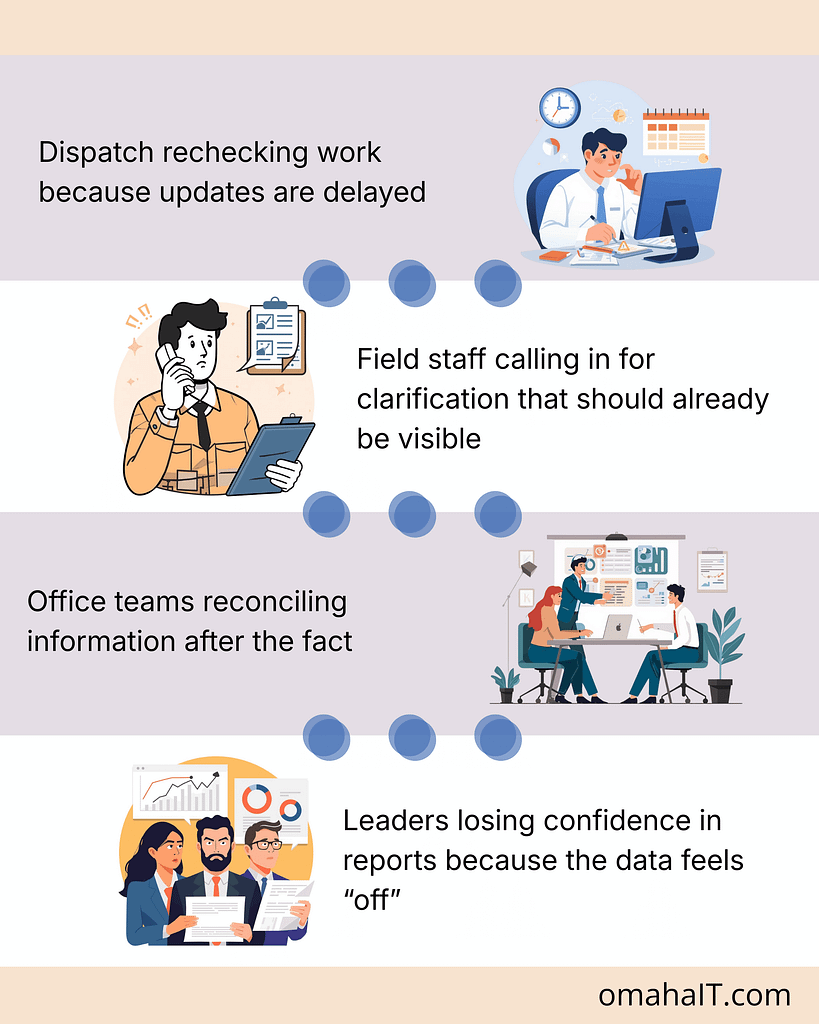
When an IT budget is too low, it doesn’t fail everywhere at once.
It fails where capacity and visibility matter most — the areas that quietly hold the entire operation together. These tend to fall into five categories:
- Operations
- Security
- Delivery and innovation
- End-user productivity
- Architecture and long-term health
The early symptoms are easy to normalize. Leaders adapt. Teams work around issues. Temporary fixes become permanent habits.
That’s why having a clear diagnostic lens matters.
Quick Diagnostic Checklist: Early Warning Signs
If several of these sound familiar, it’s a strong indicator that underfunding is already affecting operations.
Frequent outages or long time to repair
When systems fail more often — or take longer to recover — it usually signals underinvestment in infrastructure, monitoring, redundancy, or vendor support. The cost isn’t just downtime. It’s lost confidence and accumulated disruption.
Rising number of unresolved security alerts
Alerts that stay open, patches that slip, and security tasks that get deprioritized are classic signs of an underfunded security operation. This isn’t about negligence. It’s about insufficient tooling, staffing, or time.
Growing project backlog
When new initiatives keep getting pushed “to next quarter,” it often points to a capacity gap. Teams are fully consumed keeping things running, leaving no room for improvement, automation, or innovation.
Rising technical debt
Deferred upgrades and postponed maintenance feel harmless in the moment. Over time, they increase complexity, raise future costs, and make every change harder than it should be.
Individually, these issues seem manageable. Together, they paint a clear picture of an IT budget that’s stretched too thin.
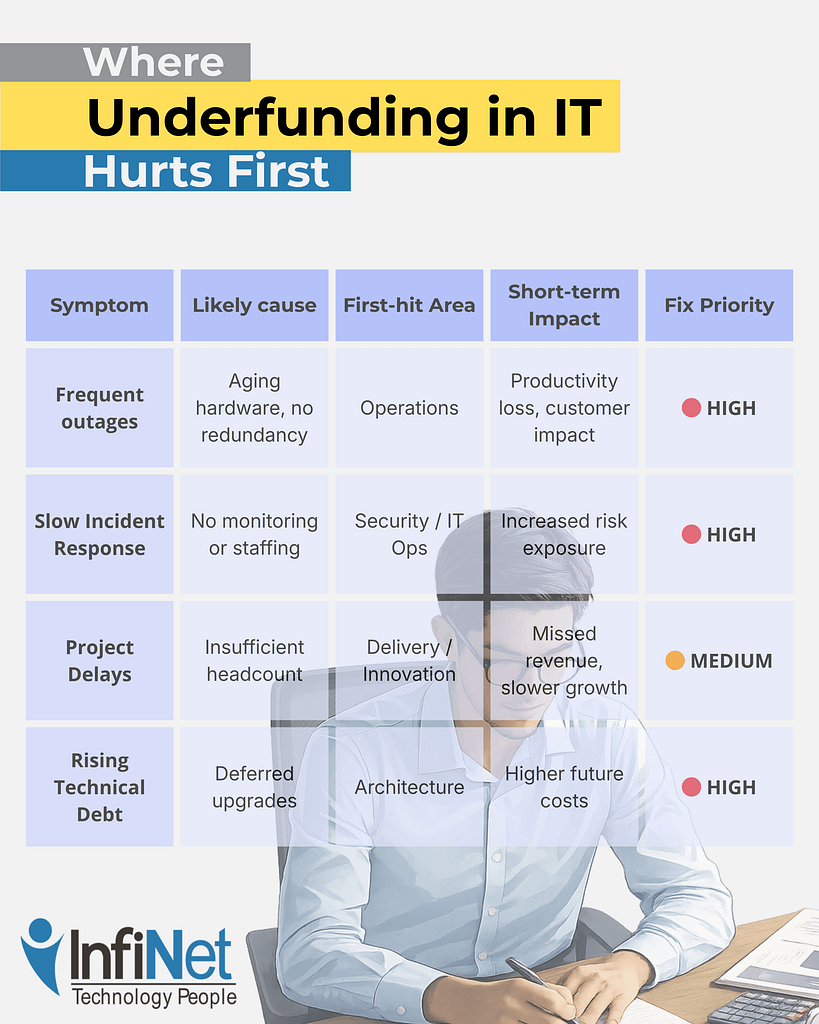
Underfunding tends to hit the same areas first because they absorb risk on behalf of the rest of the business.
As you can see, patterns are important here.
Security and availability are usually affected first — not because they’re unimportant, but because they require continuous investment to remain invisible. When funding slips, these areas quietly absorb the damage until something breaks.
By the time leadership feels urgency, the organization is often already operating in a riskier, more fragile state than it realizes.
How to Measure Whether Your IT Budget Is Too Low
Good IT budgeting isn’t about comparing spend to industry averages. It’s about understanding whether the budget supports the organization’s actual operating reality.
A few practical signals help make that visible.
Track operational KPIs
Metrics like uptime, mean time to repair (MTTR), incident volume, backlog age, and patch timelines reveal capacity gaps long before costs explode. When these trend in the wrong direction, budget pressure is usually involved.
Monitor security signals
Pay attention to how many alerts remain open, how long remediation takes, and what percentage of systems fall behind on updates. Rising numbers indicate an underfunded security posture — even if no breach has occurred.
Survey stakeholders regularly
Quarterly check-ins with leadership and staff can surface productivity drag that metrics miss. Developer velocity, business satisfaction, and helpdesk NPS often decline before formal incidents rise.
Together, these signals provide a much clearer picture than budget totals alone.
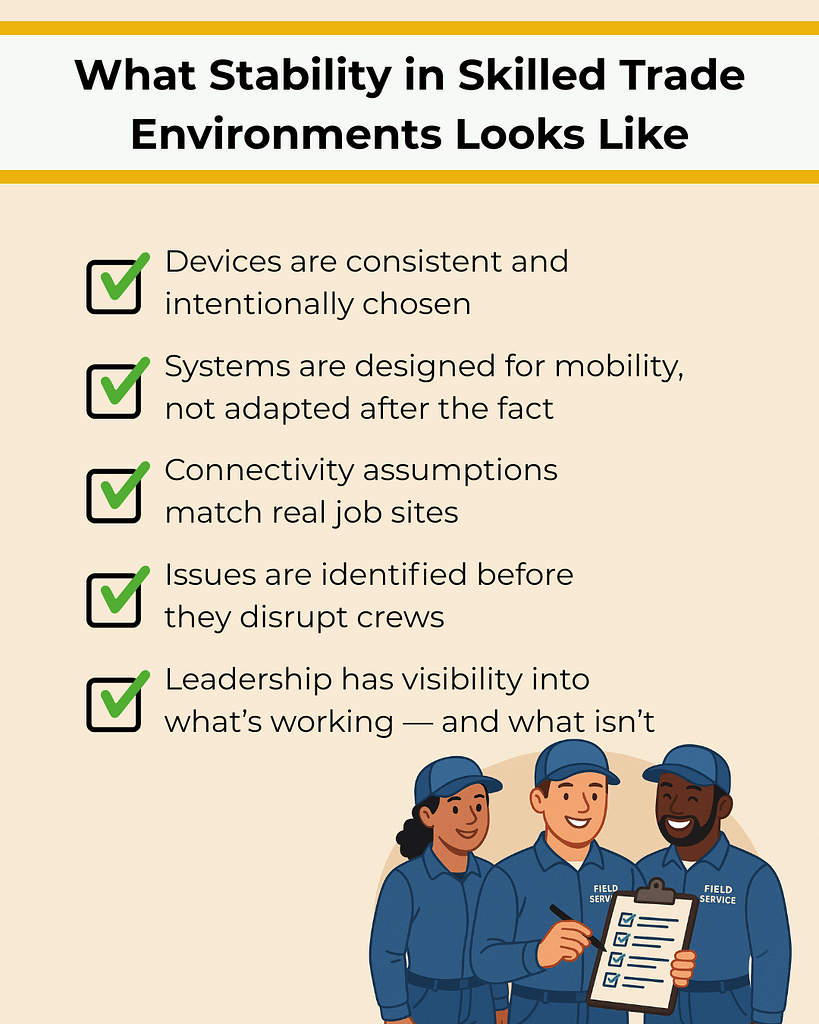
Decision Guide: What to Fix First
When underfunding becomes visible, the instinct is often to spread money thinly across everything. That usually makes the problem worse.
A more effective approach is triage.
1. Stabilize security and availability
Gaps here create the largest short-term risk. Address monitoring, patching, alert ownership, and system resilience first.
2. Restore visibility
Without clear insight into what’s happening, teams operate reactively. Investing in observability and ownership often delivers outsized returns.
3. Add intentional capacity
This doesn’t always mean hiring. It can mean automation, better tooling, or clearly defined external ownership that creates breathing room.
4. Delay non-essential initiatives
Not every project deserves immediate funding. Stabilizing foundations should come before expansion.
The goal isn’t to spend more everywhere — it’s to spend intentionally where risk and friction are already accumulating.
The Trade-Offs Leaders Often Miss
Underfunding IT can feel like a conservative financial choice. In reality, it often increases long-term costs.

Deferred maintenance becomes technical debt. Delayed security work increases exposure. Overloaded teams burn out, raising turnover risk. Incidents become more expensive the longer they’re ignored.
Short-term savings are real — but so are the downstream consequences. The most costly IT problems are rarely sudden. They’re usually the result of small compromises compounded over time.
Underfunding IT can feel like a conservative financial choice. In reality, it often increases long-term costs.
Frequently Asked Questions
1. How much should a company spend on IT?
There’s no universal number. The right spend depends on risk tolerance, regulatory exposure, system complexity, and growth goals — not just company size.
2. Is outsourcing cheaper than hiring internal IT staff?
Sometimes. Outsourcing can provide access to expertise and scale without full-time costs, but it still requires appropriate funding to be effective.
3. What’s the biggest risk of delaying IT investment?
Accumulated technical debt and reduced resilience. Problems become harder and more expensive to fix the longer they’re deferred.
4. How often should IT budgets be reviewed?
At least annually, with quarterly check-ins tied to operational and security metrics — not just spend tracking.
5. How do I justify IT spend to non-technical leadership?
Frame it around risk reduction, operational stability, and capacity — not tools or features.
A Clear Next Step
If you’re unsure whether your current IT budget is truly supporting the business — or quietly holding it back — clarity usually comes from examining how well operations, security, and delivery are actually holding up.
Understanding where friction lives today is often more valuable than debating numbers in isolation.

How to Know If Your IT Budget Is Too Low — and Where Underfunding Hurts First Read More »