MFA Isn’t Enough: What Businesses Need Beyond MFA to Stay Secure
Multi‑Factor Authentication (MFA) used to be the gold standard for preventing unauthorized access. But as threat actors have evolved, many businesses are learning the hard way that MFA isn’t enough anymore.
In reality, modern breaches don’t start with someone “breaking in.” They start with someone logging in.
The latest research shows cybercriminals now routinely bypass MFA using techniques such as phishing-as-a-service, MFA fatigue, session hijacking, and token theft.
Table of Contents
Why MFA Isn’t Enough Anymore
Multi-Factor Authentication still matters. It stops a large volume of basic attacks. But professional cybercriminals don’t rely on basic tactics — and they haven’t for years.
Attackers Have Adapted Faster Than Defenses
Today’s attacks are designed specifically to defeat MFA, not avoid it.
Common techniques now include:
- MFA fatigue attacks, where users are flooded with push notifications until one gets approved
- Real-time phishing, where attackers capture login sessions and MFA tokens as they’re used
- Session hijacking, which allows access after MFA has already been completed
- SIM swapping and device compromise, intercepting one-time codes entirely

None of these rely on guessing passwords. They rely on exploiting trust, timing, and user behavior.
MFA still fires — it just fires too late.
The Attack Surface Has Quietly Expanded
Most businesses no longer operate inside a clean, controlled network.
Access now happens across:
- Cloud applications
- Hybrid and remote work environments
- Personal or lightly managed devices
- Public and home Wi-Fi networks
When MFA is applied without device controls, network context, or behavioral checks, it becomes a single gate protecting many open paths.
This is especially risky for small and mid-sized businesses, where device management and continuous monitoring are often inconsistent or fragmented.
Identity Is Now the Primary Target
Credential theft accounted for a significant portion of breaches in 2025, with billions of credentials harvested through infostealers and phishing campaigns.
Attackers don’t need malware if they can reuse valid identities.
This shift is why cyber insurance providers are no longer satisfied with “MFA enabled” as a security answer. They expect identity-aware controls that detect abuse after login — not just before it.
What Businesses Need Beyond MFA
If MFA is the lock on the door, everything below is what watches the building.
These are the layers that modern security strategies require — especially for organizations that don’t have internal security teams.
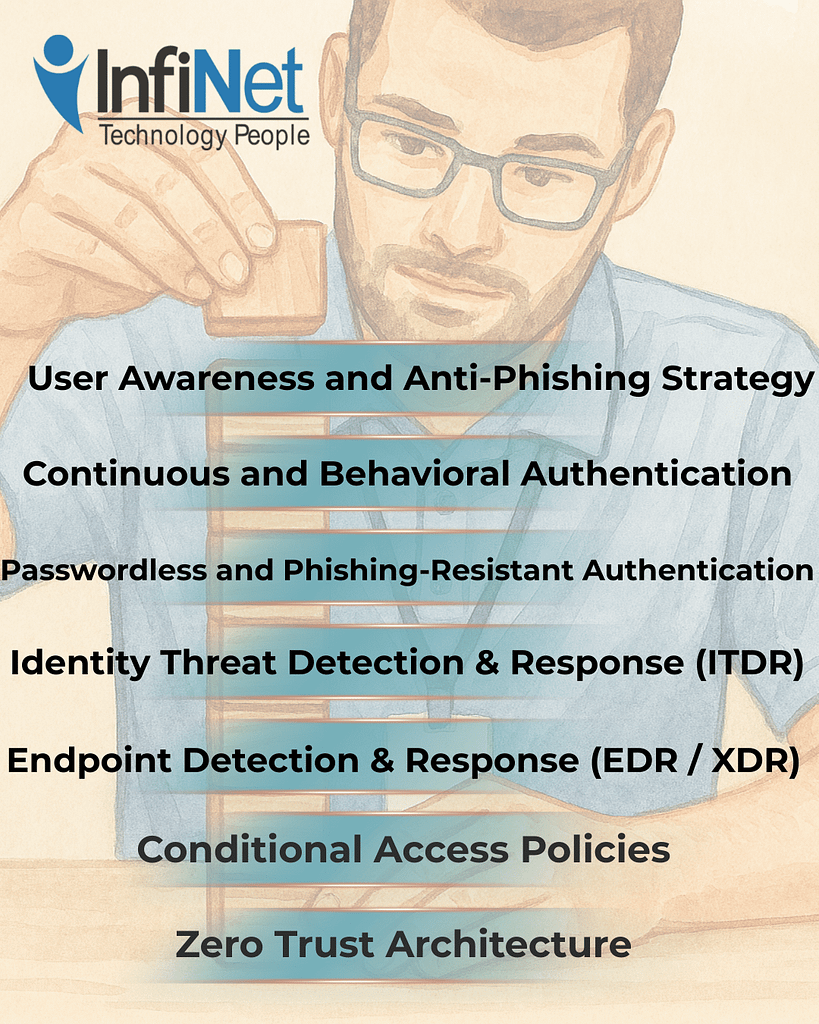
1. Zero Trust Architecture
Zero Trust operates on a simple rule: never trust, always verify.
Instead of assuming a login is safe once MFA succeeds, Zero Trust continuously evaluates:
- Who is accessing the system
- What device they’re using
- Where they’re connecting from
- Whether behavior matches normal patterns
If something changes, access is restricted or challenged again.
This approach limits damage even when MFA is bypassed and aligns with established NIST security frameworks.
2. Conditional Access Policies
Conditional Access adds context to authentication decisions.
Instead of treating every login equally, access rules can:
- Block sign-ins from unmanaged devices
- Restrict access from risky locations
- Require stronger verification for sensitive systems
The result isn’t more friction — it’s smarter friction, applied only when risk increases.
3. Endpoint Detection & Response (EDR / XDR)
When identity defenses fail, the endpoint becomes the last line of defense.
EDR and XDR tools monitor for:
- Suspicious processes
- Unauthorized privilege escalation
- Malware and lateral movement
- Indicators of session hijacking
These tools don’t wait for alerts from users. They watch behavior continuously and respond in real time.
4. Identity Threat Detection & Response (ITDR)
Identity Threat Detection focuses on what attackers do after they log in.
ITDR monitors for:
- Compromised or abused accounts
- Unusual access patterns
- Privileged account misuse
- Lateral movement across systems
This matters because modern attackers blend in. They use valid credentials, normal tools, and trusted access paths.
Without identity monitoring, breaches can remain invisible for weeks.
5. Passwordless and Phishing-Resistant Authentication
Not all MFA is equal.
Passwordless options like FIDO2 keys and passkeys reduce entire categories of attack, including:
- MFA fatigue
- Phishing token theft
- SIM-based interception
They also simplify login experiences and reduce support tickets — a rare case where stronger security improves usability.
6. Continuous and Behavioral Authentication
Static login checks assume risk ends at authentication.
Continuous authentication assumes risk evolves.
By monitoring session behavior — typing patterns, device consistency, navigation flow — systems can detect when a session no longer looks legitimate, even if credentials were valid.
This is where authentication is heading, because attackers don’t behave like real users for long.
7. User Awareness and Anti-Phishing Strategy
AI-generated phishing now mimics internal communication styles, tone, and context.
That means annual training isn’t enough.
Effective programs include:
- Ongoing phishing simulations
- Social engineering awareness
- Education tied to real attack patterns
The goal isn’t to blame users — it’s to reduce the odds that one moment of trust becomes a company-wide incident.
Why This Is Where a Managed IT Provider Matters
Tools alone don’t create security.
What businesses actually need is coordination — ensuring these layers work together and evolve as threats change.
A local Managed IT Service Provider brings:
- Continuous monitoring of identity and endpoint threats
- Policy tuning aligned with business operations
- Ongoing updates to meet cyber insurance requirements
- Rapid response when controls fail
Attackers don’t operate on office hours. Neither can effective security.

The Bottom Line
MFA is still necessary — but MFA isn’t enough.
It blocks basic attacks. It does not stop professional ones.
Modern protection requires:
✅ Zero Trust principles
✅ Context-aware access
✅ Endpoint and identity monitoring
✅ Phishing-resistant authentication
✅ Ongoing user education
The role of your MSP isn’t to sell tools. It’s to help you understand where risk actually lives — and reduce it intentionally.
If you’re relying on MFA alone, the question isn’t if it will be bypassed. It’s whether you’ll see it happen in time.
Frequently Asked Questions
1. Is MFA still worth using?
Yes. MFA stops a large number of commodity attacks. It just can’t be the only control you rely on.
2. What does “security beyond MFA” actually mean?
It means monitoring identity, devices, and behavior continuously — not just verifying a login once.
3. Why do attackers target identities instead of systems now?
Because identities provide legitimate access. Logging in is quieter and harder to detect than breaking in.
4. Do small businesses really need Zero Trust?
Yes. Zero Trust scales well for SMBs because it reduces assumptions and limits blast radius.
5. Will cyber insurance require more than MFA?
Many providers already do, especially phishing-resistant MFA and identity controls.
6. Can an MSP manage all of this without disrupting operations?
When done intentionally, yes. The goal is fewer incidents, not more friction.
MFA Isn’t Enough: What Businesses Need Beyond MFA to Stay Secure Read More »